Member-only story
The Matter Of Privacy
Among Us
Note: Please refer acronym list.1. Anonymous Signing
1.1. Multi-Signatures or Threshold Signatures
1.2. Group Signatures
1.3. Ring Signatures
2. Blinding
2.1. Homomorphic Encryption
2.2. PSI
3. Proof Systems
3.1. ZKP
3.1.1. Pedersen Commitments
3.1.2. Bulletproofs
3.1.3. ZK Challenge-and-Response
3.1.4. ZK Authentication
3.1.5. ZK Mutual Authentication
4. Anonymization
4.1. Stealth Addresses
6. The Matter Of Privacy
6.1. Privacy: What is it?
6.2. How is Privacy Assured?
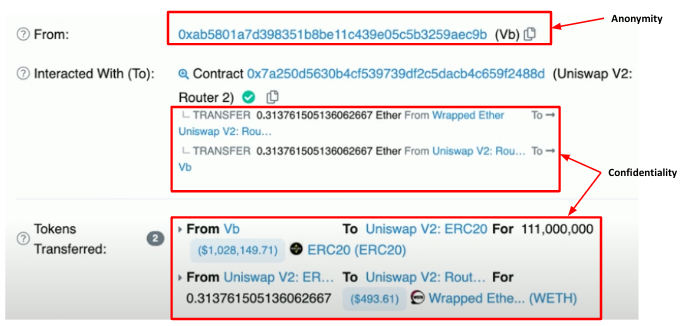
Privacy is in the matter to determine the right-to-know and the need-to-know, as well as the matter to determine who to trust and how to trust. The crux of utility and application is in the matter of proof, with the consideration of privacy, and yet the matter of proof that privacy is assured.
As all proofs are based on Assertions, how would security solutions architects assured A6?
Anonymous Signing
Multi-Signatures or Threshold Signatures
Multi-signature (Itakura and Nakamura, 1983) schemes reveal data only when certain conditions are met, i.e. an adequate number of entities (e.g., k of N, where k may be 3, N may be 5) authorize. Another option may be threshold signature or presentation, e.g. Schnorr signature, SSS (Shamir Secret sharing (1979)). """ Schnorr signature method to aggregate signers (secp256k1)
G := base point on the curve.[Sign]
A takes his private key, a random value (r_i) and a message (M), and produces a signature: (R,s ). < Keys generation >:
1. A generates private key of (x_1) and a public key (X_1):
X_1 = x_1 * G2. B generates private key (x_2) and a public key (X_2):
X_2 = x_2 * G